Regardless of your political leanings, there’s no denying the impact of the stories broken by The Guardian and The Washington Post this past week.
Edward Snowden, a 29-year-old Booz Allen Hamilton contractor assigned to the NSA (National Security Agency) is responsible for one of the most substantial national security leaks in American history. According to Snowden, the NSA has been collecting cellphone metadata on millions of Americans and using backdoor channels to gather information on foreigners who use Google, Facebook and Apple, among other service providers.
 But many policymakers and security analysts have focused on another aspect of this story: How did a contractor — who has been employed by his firm for just three months — have access to such extremely sensitive information? According to an article in The Washington Post, “By 2011, more than 4.2 million government and contract workers had security clearances, and more than a third of them had top-secret access. But little has been done to beef up the infrastructure needed to ensure that money is well spent and, more important, to protect the reservoirs of secret information the government is gathering to pursue its battle against terrorism.”
But many policymakers and security analysts have focused on another aspect of this story: How did a contractor — who has been employed by his firm for just three months — have access to such extremely sensitive information? According to an article in The Washington Post, “By 2011, more than 4.2 million government and contract workers had security clearances, and more than a third of them had top-secret access. But little has been done to beef up the infrastructure needed to ensure that money is well spent and, more important, to protect the reservoirs of secret information the government is gathering to pursue its battle against terrorism.”
Technology has made it easier to collaborate, improving workflow and increasing efficiency. But many organizations (including the NSA!) have done an inadequate job of knowing who is accessing sensitive data and for what purpose. Failing to implement the most basic security protocols will leave you open to both internal and external threats.
The good news: implementing security measures doesn’t have to hinder collaboration.
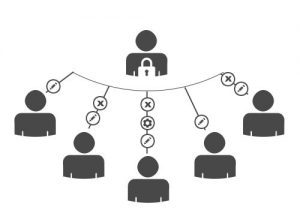
With Multiple-Users, Sogolytics allows account administrators to create and manage sub-accounts and determine permission levels, eliminating risky password sharing, confusion and inefficiency, while maintaining data privacy.
There will be times when sharing data with people inside and outside of your organization is essential to facilitating workflow. But — as recent events have demonstrated — controlling access to sensitive information is the only way to ensure it’s secure.


